When a user connects to a VPN, a “tunnel” is created. This tunnel encrypts the user’s traffic and routes it through the VPN’s servers.
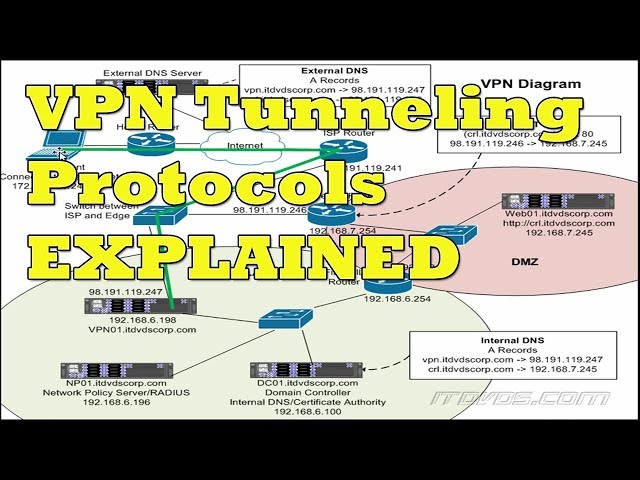 Checkout this video:
Checkout this video:
Introduction
‘Tunneling’ is a term often used to describe the process of encapsulating data packets within other packets so that they can be transmitted across a network. This process allows for the secure exchange of information between two points, as the data is effectively hidden from any third party that attempts to intercept the packets.
VPNs (Virtual Private Networks) make use of tunneling to provide a secure connection between two points, usually over the internet. By encapsulating data packets using encryption, a VPN can ensure that only the intended recipient can access the contents of the packets. This makes it an ideal solution for businesses and individuals who need to share confidential information securely.
There are a number of different types of tunneling protocol that can be used in a VPN, each with its own advantages and disadvantages. The most common protocols are PPTP (Point-to-Point Tunneling Protocol), L2TP (Layer 2 Tunneling Protocol), SSTP (Secure Socket Tunneling Protocol) and IKEv2 (Internet Key Exchange version 2).
PPTP is one of the oldest tunneling protocols, and as such is supported by a wide range of devices and operating systems. It is however considered to be less secure than newer protocols such as L2TP/IPsec or SSTP, as it uses weaker encryption algorithms.
L2TP/IPsec is a more recent protocol which offers better security than PPTP, as it uses stronger encryption algorithms. However it is not as widely supported as PPTP, and can be more difficult to set up.
SSTP is a Microsoft-developed protocol which offers good security and is widely supported on Microsoft platforms. It is however not compatible with non-Microsoft operating systems such as Linux or macOS.
IKEv2 is a relatively new protocol which offers good security and performance, and is supported on a wide range of devices and operating systems.
What is a VPN?
A VPN, or Virtual Private Network, is a private network that extends across a public network, such as the Internet. A VPN allows users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network.
How does a VPN work?
A VPN, or Virtual Private Network, allows you to create a secure connection to another network over the Internet. VPNs can be used to access region-restricted websites, shield your browsing activity from prying eyes on public Wi-Fi, and more.
Most VPNs work by routing your Internet traffic through a remote server and encrypting it before it reaches your device. The remote server acts as a gateway to the rest of the Internet, and all your internet activity appears to be coming from the IP address of the VPN server instead of your own. This lets you bypass geo-restrictions and access websites that would otherwise be unavailable to you.
What are the benefits of using a VPN?
There are many benefits of using a VPN, such as increased security and privacy, but one of the most popular reasons is to unblock websites or content that may be restricted in your country. A VPN can also be used to protect your online activity from your ISP or other third-party snoopers.
Many people use a VPN to access regionally restricted websites or content, such as BBC iPlayer or Netflix. By connecting to a VPN server in another country, you can bypass geographical restrictions and get access to the full library of content.
A VPN can also be used to improve your online security and privacy. When you connect to a VPN, all of your traffic is routed through an encrypted tunnel. This means that anyone trying to snoop on your traffic will only see gibberish, making it much more difficult for them to track you or steal your data.
What is tunneling?
Tunneling is a method of encapsulating Internet Protocol (IP) data packets within an IP datagram. Tunneling allows you to send data securely from one network to another. When you use a VPN, all of your data is sent through a tunnel. This tunnel is encrypted, which means that anyone who tries to intercept your data will not be able to read it.
How is tunneling accomplished in a VPN?
Tunneling is the process of encapsulating Internet Protocol (IP) datagrams within an IP datagram. The encapsulation is accomplished by encapsulating the original IP datagram within an additional IP header. In this way, a VPN can tunnel any type of data it desires, including regular Internet traffic (which uses the TCP and UDP protocols), as well as non-IP data such as NetBIOS traffic.
What are the benefits of using tunneling in a VPN?
Tunneling is a method of transporting data between two locations by encapsulating the data in a packet. The benefits of using tunneling in a VPN are that it eliminates the need for costly leased lines, and it can be used to connect sites that are geographically distant from each other. In addition, tunneling can be used to connect multiple sites to a single network, or to connect a single site to multiple networks.
Conclusion
In conclusion, ‘tunneling’ is a process by which data is securely exchanged between two points across a network. This is accomplished by encapsulating the data packets in such a way that they can be passed through the network without being tampered with or intercepted.
